A software system that solves specific management needs
Software Development
HZZCSOFT custom application development services cover third-party integration, mobile, desktop, web and anything. HTML5 certified back-end developers have the ability to build and support technologies for user oriented components of your website. We are good at customized development of various interaction and business systems, including H5 and mobile phones
LET'S TALK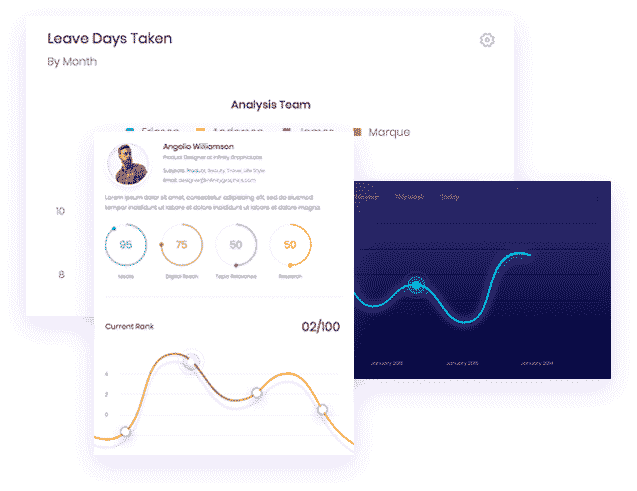
Tampa Web Application Development
What is SaaS? The SaaS (Software as a Service) model allows users to access, use, and pay for software online without desktop installation, further maintenance, or integration issues. SaaS provides customers with off the shelf software through web browsers or mobile applications. SaaS application development service is a process in which professional software developers plan, develop and deliver SaaS solutions. How long does it take to build a SaaS product? How much does it cost to build a SaaS platform? Is SaaS safe? Contact us for saas customized development solutions.
Mobile App Development
If you want to know how hiring software developers can benefit your business, please continue to read this website to explore some ways your enterprise can obtain huge benefits from software development companies. For details, please contact us through the customer service window at the lower right corner
Dedicated Development Team
Software customized application development service, we will help you realize a more complex software vision through our superior full cycle customized application development service. So you can focus on providing a slightly incredible user experience that sets you apart from the competition.