A software system that solves specific management needs
Software Development
HZZCSOFT custom application development services cover third-party integration, mobile, desktop, web and anything. Web application development enables Web based projects to execute and operate like mobile applications. Web applications attract users and give priority to responsive interaction, but they are still delivered through the Internet through the network. It can be said that Web application development is more or less the cool brother of Web development. Web development is the reason why you are on this page, but Web application development is the way to write all these high priority first. Contact us to get your Web software customization development case
LET'S TALK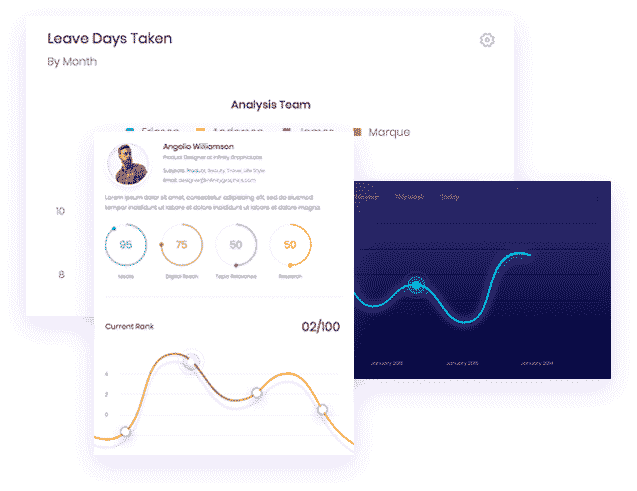
Madeira Web Application Development
User interface/user experience development, how to make your users feel comfortable after browsing your digital assets, has a great impact on your business success. We will help you get a lasting experience through unmatched UI/UX development. User experience is the advantage of our software customization development service.
Mobile App Development
We considered multi tenancy, scalability, self-service/automation, third-party integration, reporting and business indicators. By evaluating these factors, our goal is to provide better functional applications, university technology stacks, including programming languages for Web application development software.
Dedicated Development Team
Network application mask, clean script, pleasant user experience and changes are the only unchanged. Therefore, our engineers constantly hone their skills in improving UI implementation and ensuring impeccable product quality