A software system that solves specific management needs
Software Development
HZZCSOFT custom application development services cover third-party integration, mobile, desktop, web and anything. Application development insights. Read our exclusive and insightful blog about application development, which will enable you to understand its importance and more clearly understand the theme: make the right decision, and contact us at the right time for more information
LET'S TALK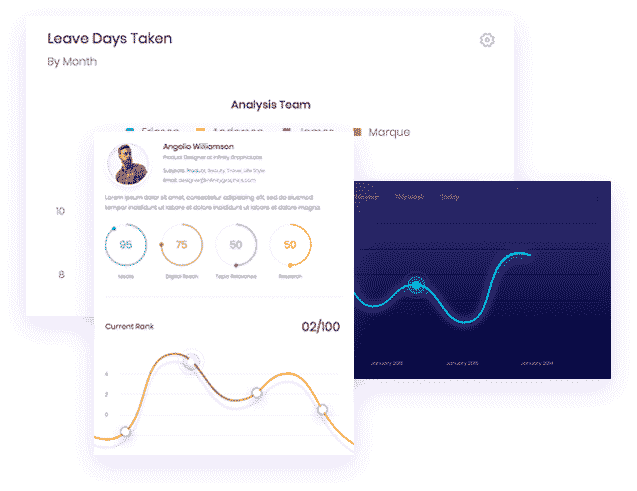
Mabaruma Web Application Development
Testing and quality assurance. Before going online, we will strictly test every screen, every framework, and every function to ensure a seamless user experience. Launch and enter the market. With a more comprehensive go to market strategy based on market needs and demands, we will launch your applications and measure results for continued success..
Mobile App Development
Including native mobile app applications, mobile app compatible web-based applications and hybrid applications. We use internal modules and components developed over time for enterprise level device and user management and remote application management. Our team has rich experience in updating tools and technologies:
Dedicated Development Team
We are eager for our software customization architect to cooperate with your software project to upgrade your user experience to a new level. Please contact us to submit your software products or enterprise information needs, and let us issue a quotation plan for you